Investigate Every Alert.Hunt Every Advisory.Document Every Action.
AI for Enterprise Security: your tools, your workflows, your data. Nothing leaves your environment.
The Reality of Modern Security Operations
4,330
Average daily alerts per organization. Only 37% are investigated.
24+ hrs
To manually analyze a single threat intelligence advisory
63%
Of alerts close without a documented investigation
How It Works
Four steps. Zero manual effort.
From data to documentation: fully autonomous, fully auditable.
The Platform
Agents do the work. Analysts make the calls.
Crogl handles the investigation: gathering context, querying your tools, and cross-referencing data across alert and threat advisories. Every action is documented. Every finding is surfaced.
Your analysts receive complete, auditable investigations ready for a decision.
Crogl handles the investigation. The analyst makes the call. Every action is visible, modifiable, and documented. Analysts review, override, and learn from every step Crogl takes.
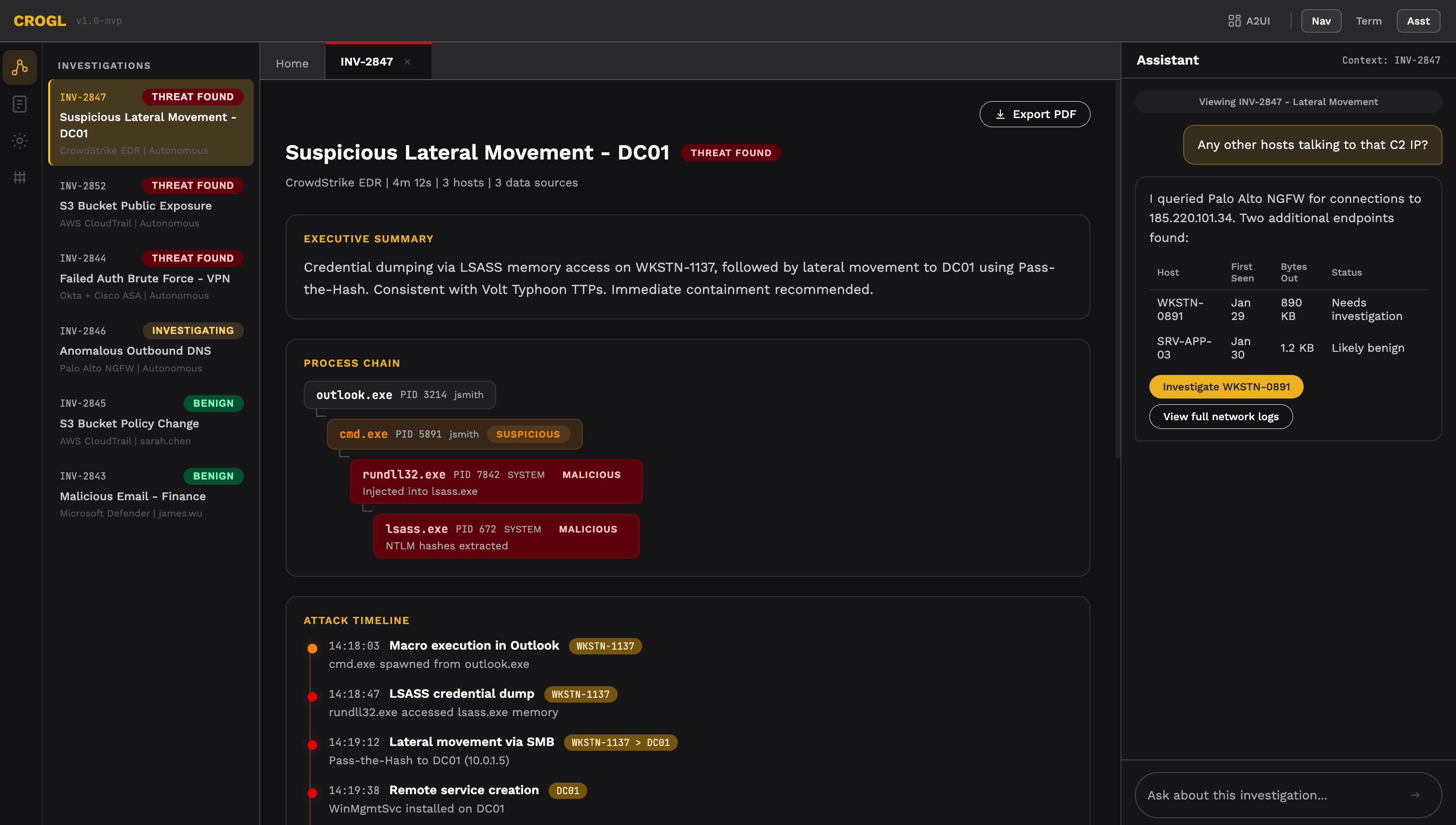
Crogl detected credential dumping via LSASS, traced lateral movement to DC01, and identified two additional compromised hosts autonomously.
Why Crogl Is Different
Customer Managed
Deploy on-premises, in your private cloud, or fully air-gapped. Crogl runs inside your infrastructure — no data leaves your environment, no exceptions. This isn't a configuration option. It's the architecture.
Neurosymbolic system
Uses knowledge graphs, large language models, agents, and intelligence from security best practices to drive the best operational outcomes for your security teams.
Works With Your Stack. Today.
Integrates with your SIEM, EDR, ticketing, and data lake on day one. No schema normalization. No recoding. If your data is there, Crogl can query it.
Transparent and Auditable
Every investigation, every query, every finding, every decision is fully documented and auditable. Whether an alert closes as benign or escalates to your team, the complete record is in your ticketing system. Compliance teams get what they need.
Built for Real SOC Problems
Alert Triage & Investigation
Crogl investigates every alert your team receives, from the routine to the unprecedented, so analysts focus only on what requires human judgment.
SIEM Migration
Move to any SIEM without rebuilding playbooks, remapping schemas, or losing a single detection use case. Crogl abstracts your investigation logic from your SIEM entirely.
Threat Coverage
A user logs in from New York at 2:00 PM. Four minutes later, the same user logs in from Prague. Crogl queries your SIEM, EDR, identity provider, and threat intelligence feeds in native format. The investigation is on the analyst's desk before the alert reaches the queue.
Works With Your Existing Stack
“No schema normalization. No recoding. Connect and investigate.”
Join the Crogl Community
Practitioners sharing what actually works in the SOC. No vendor pitches.
Get Started
See Crogl investigate an alert from your environment.
Install on your workstation. Connect your data sources. Run your first investigation against real alerts in your environment.
Download
Deployed Where the Stakes Are Highest
⚡
Major US Electric Utility Company
< 1 hr
CRISP report analysis
Previously: 24+ hours per report
Critical infrastructure protecting the grid. A missed alert or a delayed analysis isn't a performance issue. It's an operational risk.
🏛
U.S. Defense Agency
1,000+
Alerts attended daily
Previously: hundreds uninvestigated every day
Air-gapped. Classified environment. Extreme security requirements. Crogl investigates every alert without a single byte leaving the environment.
🏦
Fortune 500 Financial Institution
Minutes
Cross-lake investigations
Previously: ~1 hour per investigation
Analysts no longer need to know every schema, every query language, every data location. Crogl does the navigation. They make the call.